Certificate lifecycle on autopilot.
Discover certificates across your network, automate issuance and renewal via ACME and Microsoft AD CS, and distribute to your entire infrastructure. One platform, zero missed renewals.
Everything you need for certificate management.
From issuance to distribution, CertAutoPilot handles the full certificate lifecycle with enterprise-grade security and compliance.
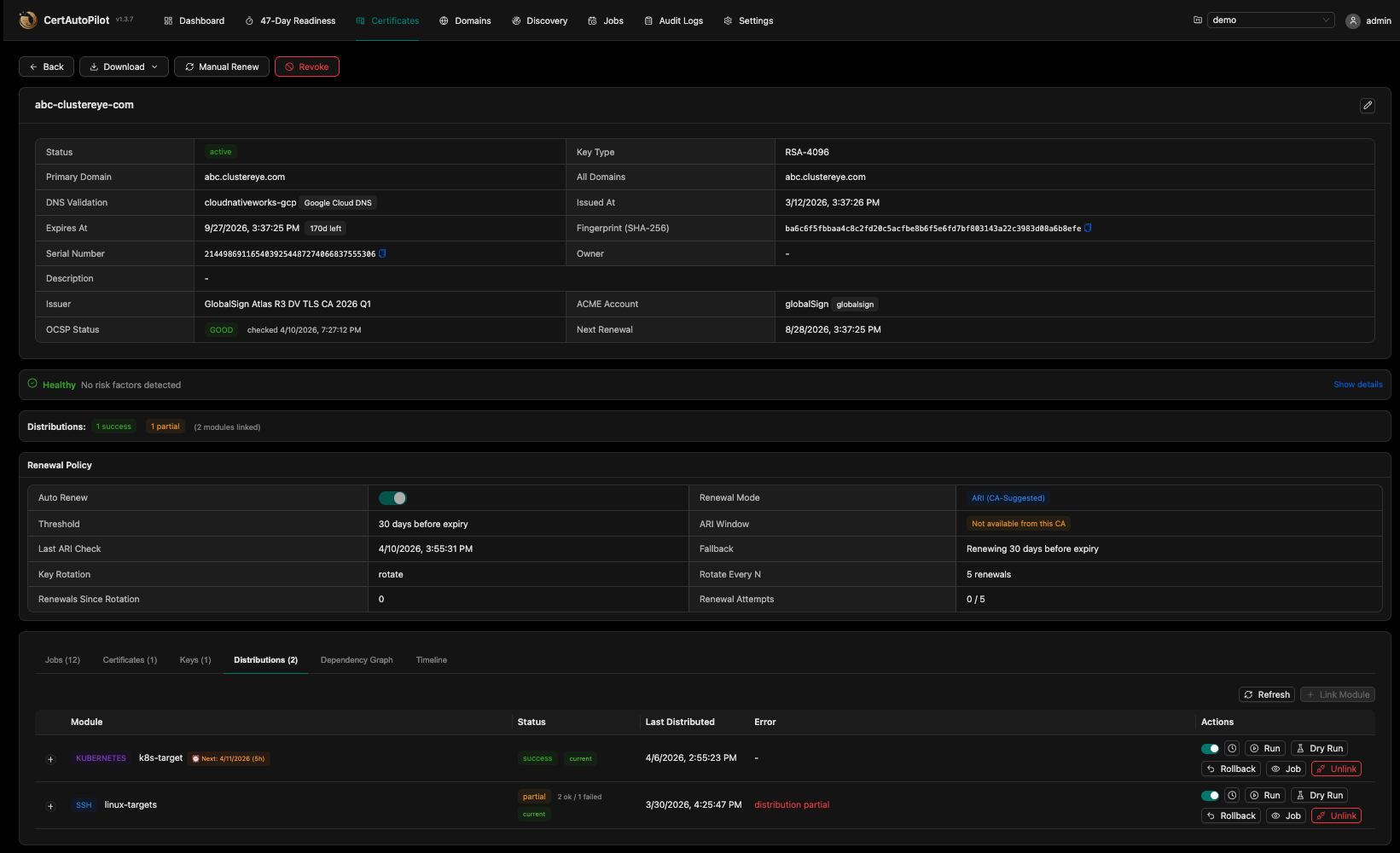
Certificate Lifecycle Automation
Automated issuance, renewal, and revocation via ACME v2 and Microsoft AD CS. Supports Let's Encrypt, Google Trust Services, Sectigo, DigiCert, and more.
Certificate Discovery
Scan networks and monitor CT logs to build a complete inventory. Automated security findings, drift detection, OCSP/CRL checking, and managed transition.
Multi-Target Distribution
Deploy certificates to 10 built-in targets with fan-out execution, dry-run validation, and automatic rollback. Agentless architecture — no agents to install.
Approval Workflows
Request/approve/reject flow with preflight warnings and governance controls. Self-approval blocked. Integrated with the notification system.
Multi-Tenant RBAC
Owner, Admin, Operator, Viewer hierarchy with project-scoped permissions. LDAP/AD integration, 2FA, JWT with refresh-token reuse detection.
Domain Monitoring
WHOIS expiry tracking, SPF/DMARC/DNSSEC health checks, and DNS propagation monitoring across your domain inventory.
Tamper-Proof Audit
HMAC-chain integrity verification on all audit entries. Event sourcing for complete certificate lifecycle timeline. RFC 5424 syslog forwarding.
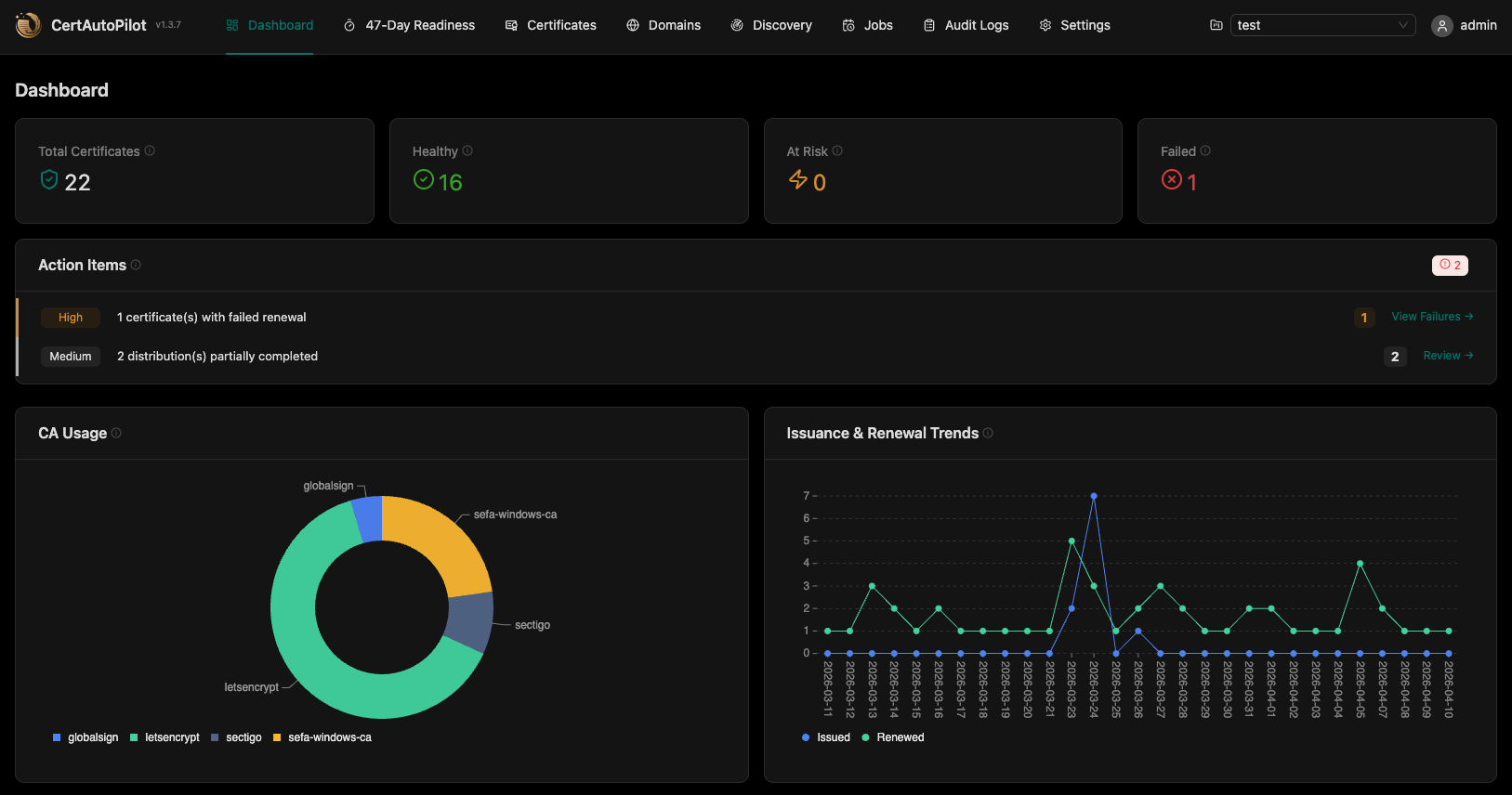
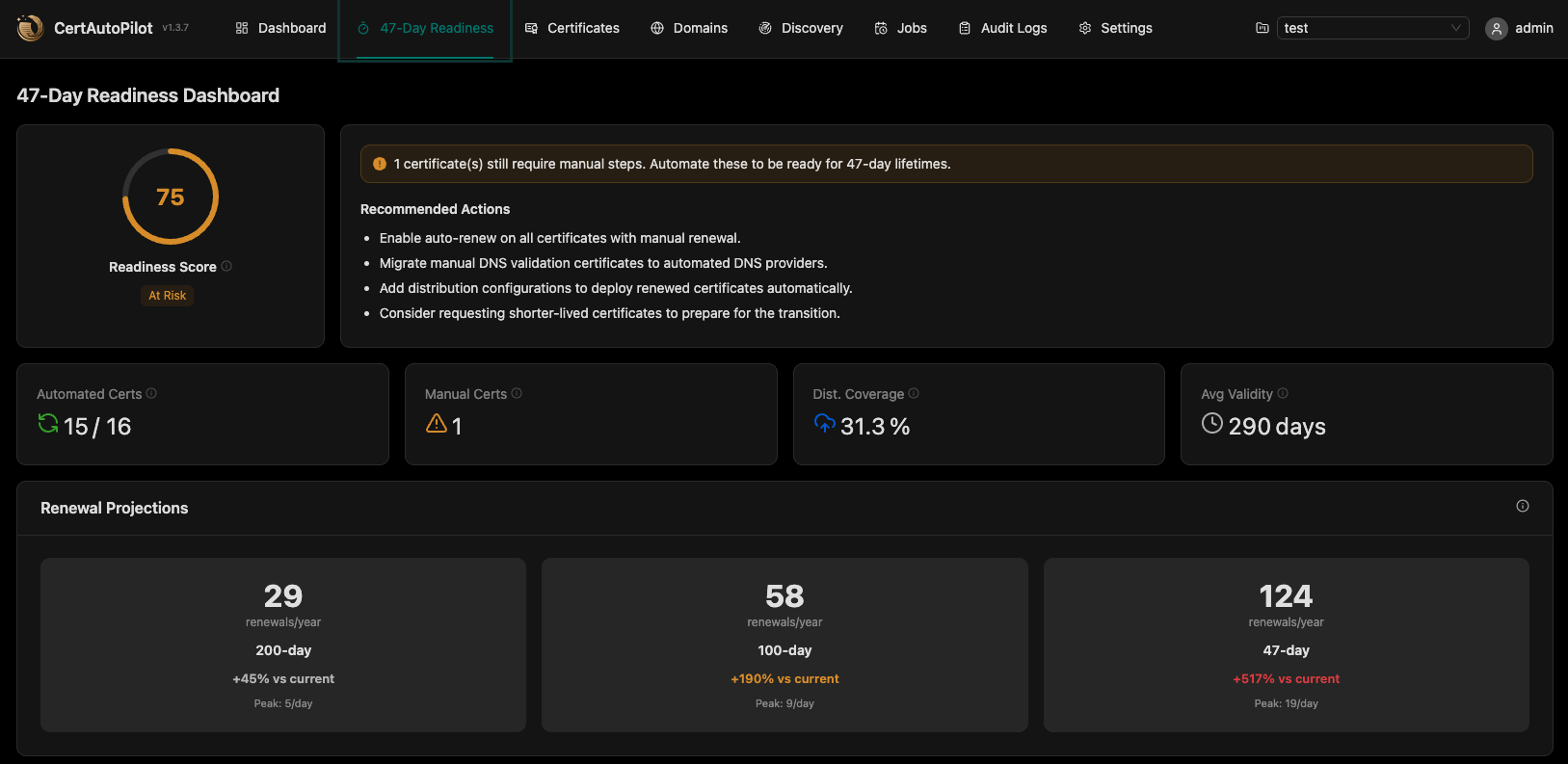
Dashboard & Observability
Prometheus metrics, OpenTelemetry tracing, and 47-day readiness scoring. CA usage breakdown, renewal trends, and live action items.
API & Automation
190+ REST API endpoints with scoped API keys, Go template variables, webhook events, and full CI/CD integration. Everything in the UI is in the API.
PQC Readiness
Classify Post-Quantum Cryptography readiness per certificate across your inventory. Identify which certs are vulnerable today and plan migration.
Envelope Encryption
AES-256-GCM with per-field DEK/KEK architecture. Private keys, credentials, and secrets encrypted at rest with versioned key management.
Smart Notifications
Email, Slack, and Microsoft Teams alerts for 18 event types with templates. Renewal failures, expiry windows, distribution status, audit events.
Find every certificate in your network.
Scan networks, monitor Certificate Transparency logs, and check OCSP/CRL revocation status. Identify risks, track changes, and transition to managed lifecycle.
Network Scanning
Define IP ranges and ports. The discovery engine connects to each endpoint, retrieves TLS certificates, and builds a real-time inventory with cipher suite analysis.
Security Findings
Actionable findings with severity levels and remediation guidance. Weak ciphers, deprecated TLS, expiring certificates, and PQC vulnerability assessment.
Drift Detection
Schedule recurring scans to detect certificate replacements, issuer changes, and key rotations. Track change history and get notified on drift events.
From configuration to delivery.
Set it up once. CertAutoPilot handles the rest — continuously, reliably.
Discover & Configure
Scan your network for existing certificates. Configure CA providers, DNS credentials, and distribution targets.
Issue Certificates
Request certificates via ACME or Microsoft AD CS with policy enforcement and optional approval workflows.
Distribute
Deploy to SSH, Kubernetes, IIS, F5, NetScaler, Vault, and cloud providers with dry-run validation.
Auto-Renew
The scheduler monitors expiry windows and automatically renews and redistributes before certificates expire.
Certificate authorities, DNS providers,
and native integrations.
Connect to your existing infrastructure with native integrations — no adapters or agents required.
— Certificate Authorities
— DNS Providers for Challenge Validation
— Distribution Targets
— Integrations & Observability
How CertAutoPilot stacks up.
Self-hosted, agentless, and built for the post-quantum, 47-day-renewal era.
| Feature | CertAutoPilot | Venafi TLS Protect | Sectigo CM | ManageEngine KMP |
|---|---|---|---|---|
| Self-Hosted / On-Premise | ✓ | ✓ | Cloud only | ✓ |
| ACME Protocol | ✓ | ✓ | ✓ | ✗ |
| Microsoft AD CS | ✓ | ✓ | ✗ | ✓ |
| Distribution Modules | 10 built-in | Custom adapters | Limited | Agent-based |
| SSH · K8s · IIS · WinRM · F5 · NetScaler · Vault · Webhook · Huawei · SMTP | ✓ All native | Partial | ✗ | Partial |
| Certificate Discovery | ✓ | ✓ | ✓ | ✓ |
| 47-Day Readiness (SC-081) | ✓ | ✗ | ✗ | ✗ |
| PQC Readiness Assessment | ✓ | Roadmap | ✗ | ✗ |
| Agentless Architecture | ✓ | Agent required | ✓ | Agent required |
| HSM Key Storage (PKCS#11) | ✓ SoftHSM2 / CloudHSM / Luna / Fortanix | Paid tier | Cloud-managed only | ✗ |
| KEK Rotation (Fleet-Aware) | ✓ Zero-downtime | Paid tier | ✗ | ✗ |
Frequently asked questions.
Automate your certificates.
End the renewal panic.
See how CertAutoPilot can discover, manage, and distribute certificates across your entire infrastructure.
